When you have effectively finished one of many processes previously mentioned, you need to be capable to log into your distant host with no
The generation system begins. You'll be requested where you want your SSH keys to be saved. Push the Enter crucial to simply accept the default spot. The permissions on the folder will safe it for the use only.
Observe that the password you should give Here's the password for your consumer account you are logging into. It's not the passphrase you might have just produced.
Automatic duties: Simply because you don’t really need to form your password anytime, it’s easier to automate tasks that require SSH.
SSH keys str vital pairs according to community essential infrastructure (PKI) technology, They may be utilized for digital identification authentication and encryption, to offer a protected and scalable way of authentication.
If you end up picking to overwrite the key on disk, you will not be capable of authenticate utilizing the past vital anymore. Picking “Indeed” is really an irreversible damaging method.
SSH keys are designed and used in pairs. The 2 keys are connected and cryptographically secure. One is your general public essential, and the other is your private key. They are really tied on your user account. If multiple people on an individual Pc use SSH keys, they can Every single receive their very own set of keys.
four. Pick which PuTTY product functions to set up. If you do not have any unique demands, stick with the defaults. Simply click Next to progress to the following monitor.
Don't attempt to do anything with SSH keys right until you may have verified You may use SSH with passwords to connect with the target Personal computer.
in the look for bar and Test the box close to OpenSSH Shopper. Then, click on Up coming to install the feature.
However, SSH keys are authentication qualifications identical to passwords. So, they have to be managed rather analogously to user names and createssh passwords. They should have a proper termination process so that keys are removed when no more wanted.
In almost any more substantial Business, usage of SSH crucial administration solutions is nearly essential. SSH keys must also be moved to root-owned locations with suitable provisioning and termination procedures.
Handling SSH keys may become cumbersome once you have to utilize a second essential. Traditionally, you'd probably use ssh-increase to shop your keys to ssh-agent, typing while in the password for every key.
When generating SSH keys underneath Linux, You need to use the ssh-keygen command. It's a Software for developing new authentication crucial pairs for SSH.
 Brandy Then & Now!
Brandy Then & Now! Mackenzie Rosman Then & Now!
Mackenzie Rosman Then & Now! Gia Lopez Then & Now!
Gia Lopez Then & Now!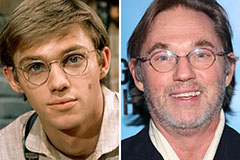 Richard Thomas Then & Now!
Richard Thomas Then & Now! Terry Farrell Then & Now!
Terry Farrell Then & Now!